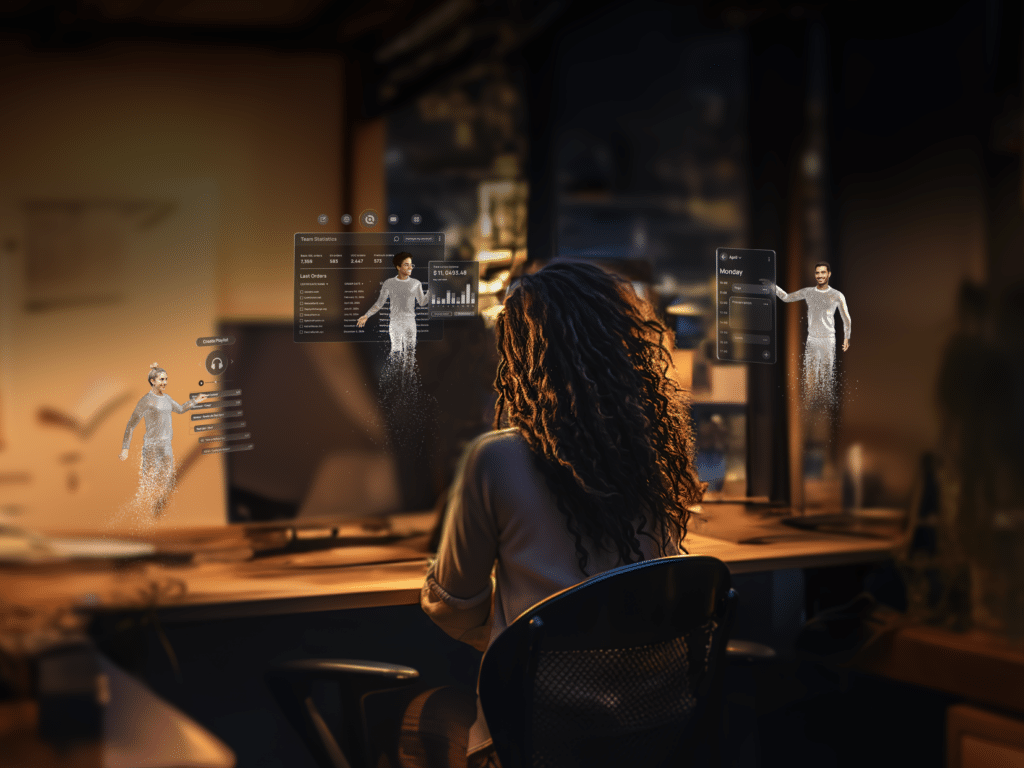
Meet the Natural User Interface (NUI) by D-ID. The interface that humanizes interactions with everything digital. Build interfaces that understand the needs of users and can be communicated with effectively. No typing, no clicking, just face-to-face conversation.
While tech has advanced exponentially in the 21st century, interfaces have remained stagnant since the 1980s. Until now.
Textual User Interface
Graphical User Interface
Natural User Interface







NUI’s brain is powered by the latest in Large Language Models along with your provided knowledge, and with emotion analysis. It understands what you say – and how you feel, and is an expert in your provided context.
NUI’s face utilizes high-quality live video streaming and facial expression generation to appear and behave like a real human with emotional feedback. You can use one of our default faces – or simply upload your own.
NUI’s voice is generated in high-fidelity audio with tonal inflection to sound naturally human in any language. You can upload your own voice, or select a default voice from our diverse library.
Check out the resources below to learn about the next stage of interface evolution.